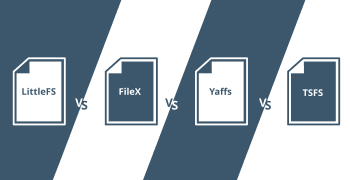
Comparing 4 Popular Embedded File Systems for NOR and NAND Flash
In this article, we discuss 4 popular file systems for both NOR and NAND flash, commonly used in bare metal and RTOS-based embedded systems: LittleFS, Yaffs, FileX and TSFS. We provide a brief description of each file system and compare their performance, RAM consumption and other specific advantages and limitations. There are plenty of other … Read more